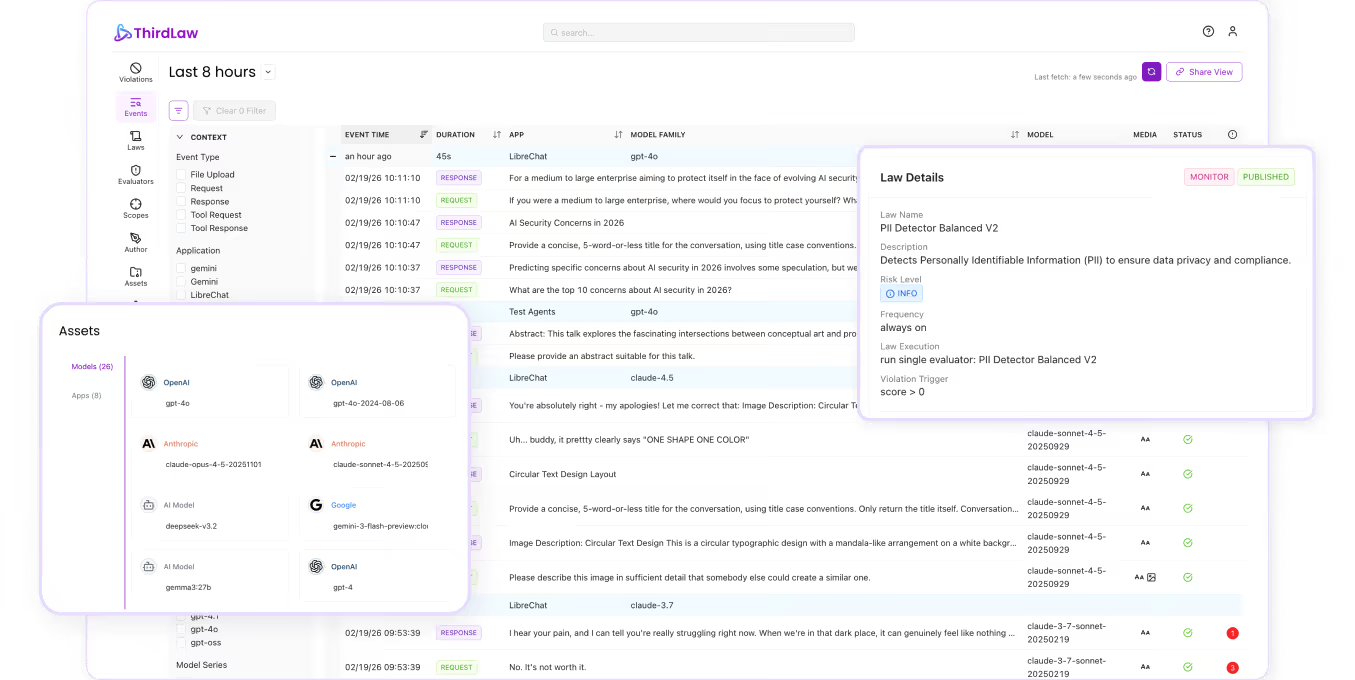
Make AI Obey Enterprise Policy
Enforce policy at runtime across prompts, responses, tool calls, and agent actions, with investigation-ready traces
Open Letter from Our CEO
Why Security and IT Need a Control Layer for AI
Dear Security and IT leaders,
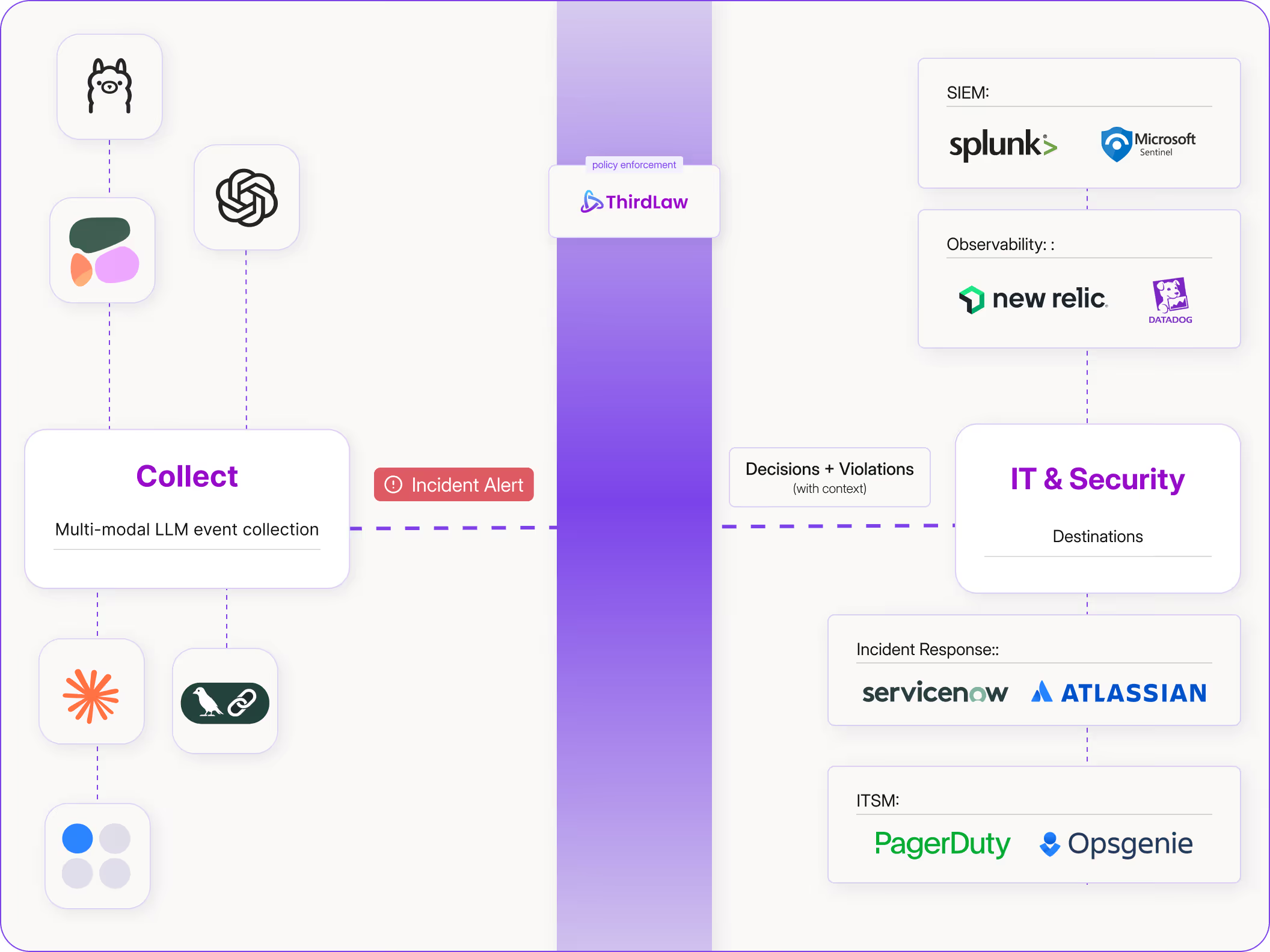
AI incidents don’t look like outages. They’re decisions that cross policy lines: a single prompt can trigger data exposure, policy-violating output, or an agent taking an irreversible step. Logs can explain it after the fact, but they don’t prevent it. That’s why enterprises need a control layer for AI, not just observability.
ThirdLaw exists to answer one question in the moment: Is this AI behavior OK? We evaluate every prompt, response, tool call, and agent action against enterprise policy, then block, redact, reroute, or escalate in real time. With ThirdLaw, you can enforce your policy at runtime, with end-to-end incident traces and audit-ready proof of what was enforced.
Sincerely,
.avif)

The AI Control Layer
Evaluate behavior in context, then intervene when it crosses the line.
Update Policy Without Code
Define policy in plain language and update enforcement without code changes.
Unsafe Output
Prevent prohibited or out-of-scope responses before they reach users.
Acceptable Use
Enforce behavior limits by role, app, and environment.
Runaway Agents
Catch loops and abnormal patterns; throttle or escalate in real time.
Tool Permissions
Allow or deny tools by role, environment, and task context.
Action Approvals
Require human review for exports, deletions, and irreversible changes.
MCP Server Governance
Restrict risky parameters and data flows in tool inputs and outputs.
Agent Chains
Track agent chains and enforce boundaries across delegated steps.
PII Protection
Detect and redact sensitive data in prompts and outputs.
Secrets Protection
Prevent exposure of API keys, tokens, and passwords through AI.
IP Protection
Stop internal documents and proprietary data from being revealed.
RAG and Tool DLP
Apply DLP to retrieval snippets and tool inputs/outputs.
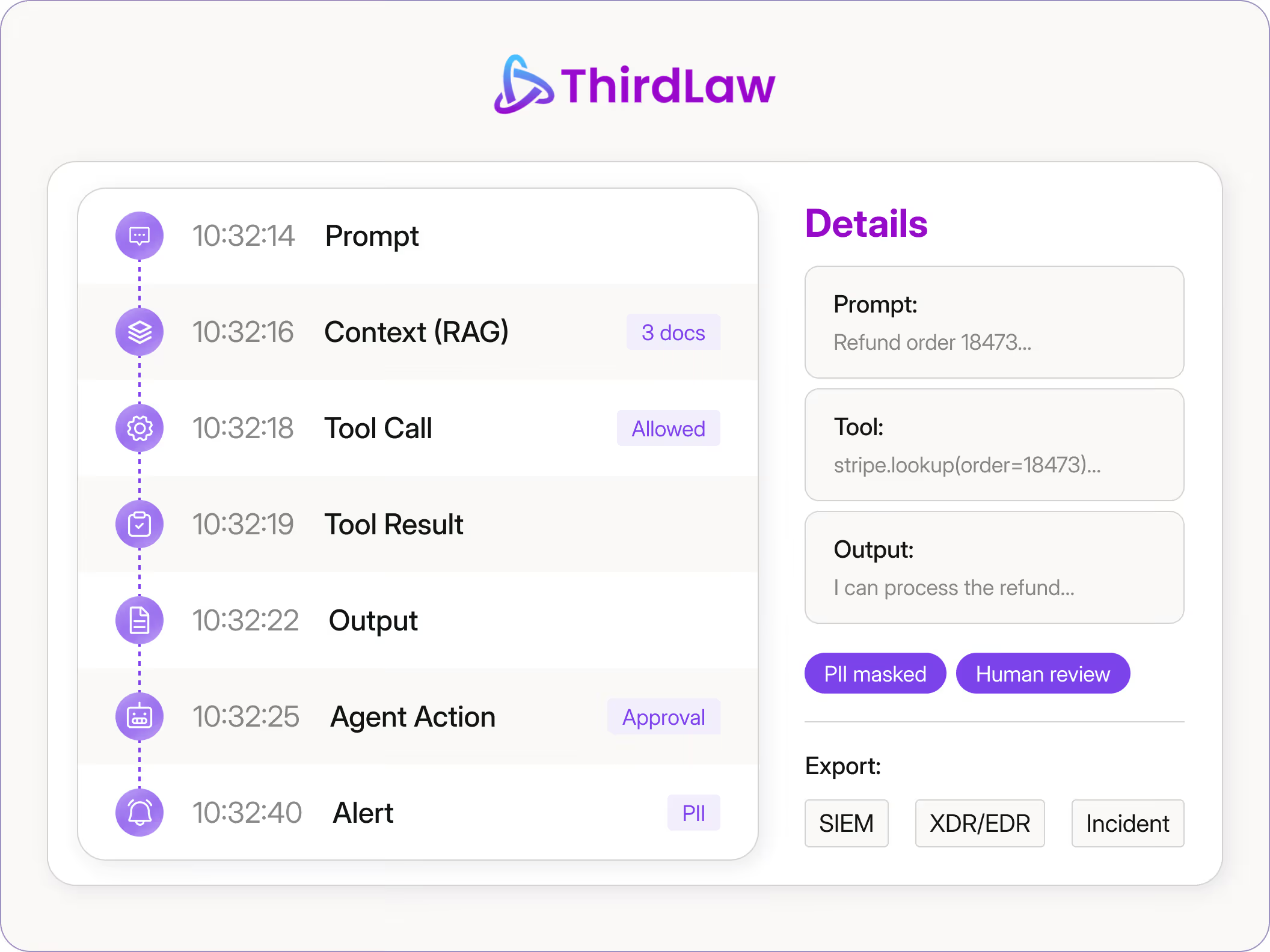
Session Replay
Rebuild timelines across prompts, context, outputs, and actions.
Tool-Call Forensics
Trace which tools were invoked, in what order, and with what data.
Evidence Export
Package findings for incident workflows and reporting.
Root-Cause Analysis
Explain why a violation occurred and what changed (rules, models, tools, context).
No-Code Policy Authoring
Define acceptable behavior in plain language and apply it consistently.
Policy Versioning
Track what changed, who approved it, and when it took effect.
AI Inventory
Discover where AI is used and ensure controls apply consistently.
Third-Party AI Oversight
Apply rules to external models and copilots, and record what they did.
Partner Ecosystem and Recognition:



Why ThirdLaw
A unified layer for AI oversight. Centralized policy, evaluation, and intervention.
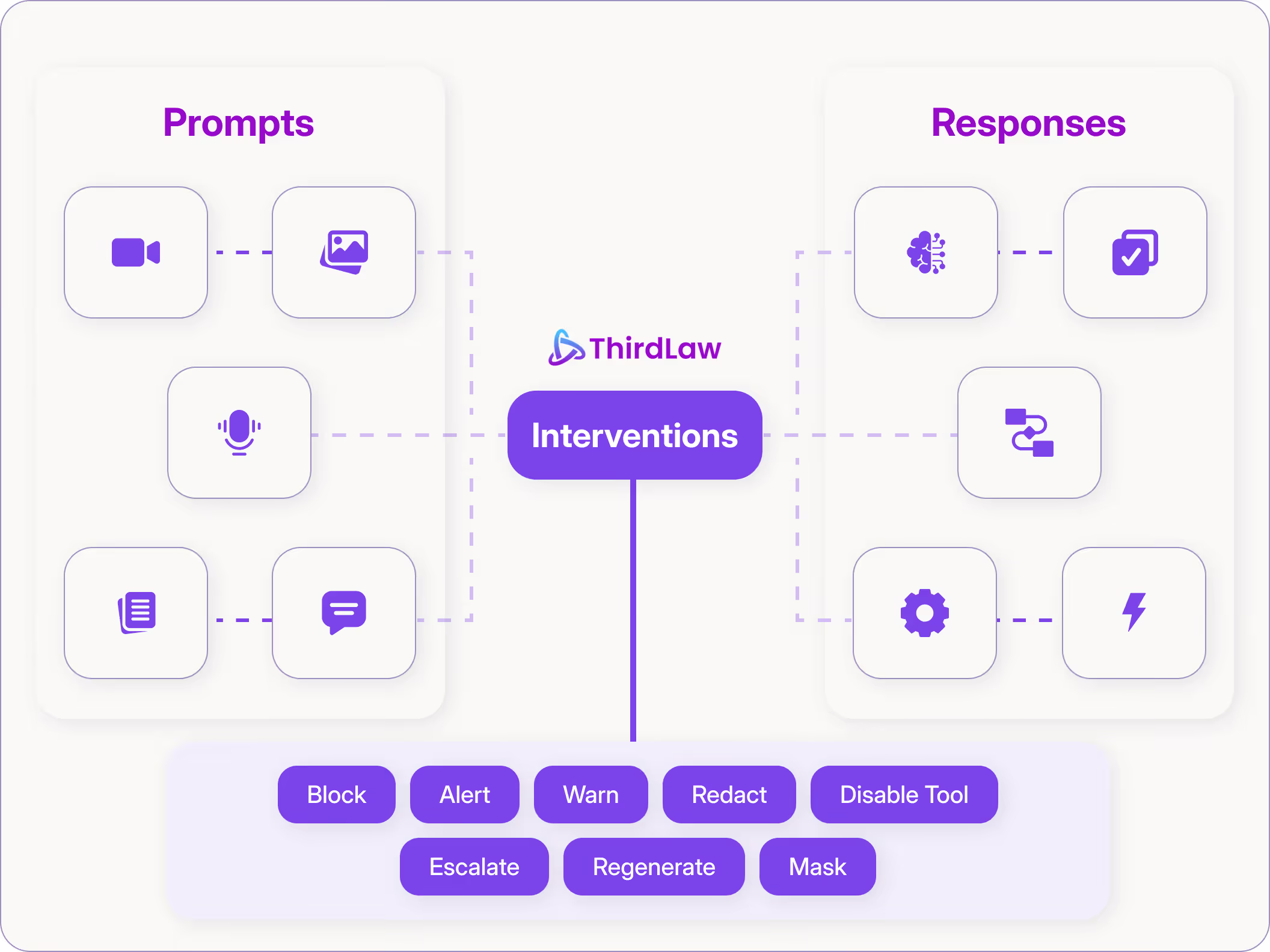
Runtime Policy Enforcement
Detect violations in-line and block, redact, or reroute in real time.
End-to-End AI Traces
Search prompts, outputs, tool calls, and agent actions in one session timeline.
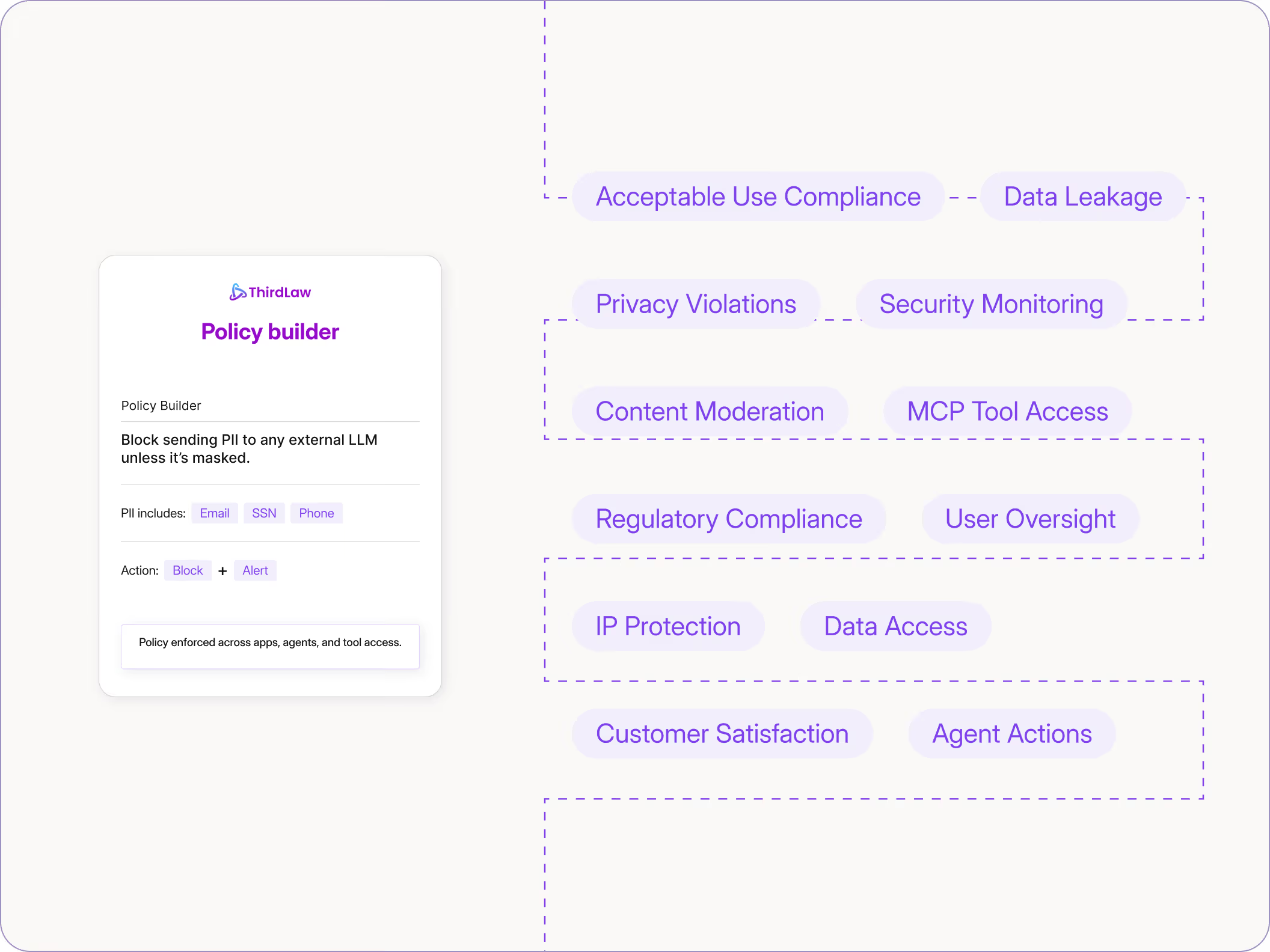
Policies in Plain Language. Zero Code.
Security and IT control policy from one place, without app-by-app updates.
.avif)
Keep Sensitive Data Out of AI
Prevent exposure of PII, secrets, and proprietary data across prompts, outputs, retrieval, and tool use.
